Wireshark provides a variety of options for exporting packet data. This section describes general ways to export data from the main Wireshark application. There are many other ways to export or extract data from capture files, including processing tshark output and customizing Wireshark and TShark using Lua scripts.
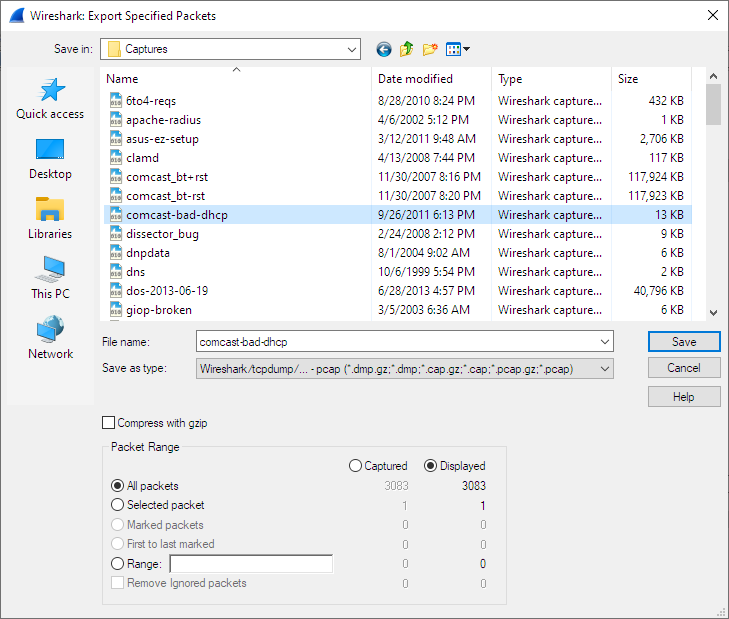
This is similar to the “Save” dialog box, but it lets you save specific packets. This can be useful for trimming irrelevant or unwanted packets from a capture file. See Packet Range for details on the range controls.
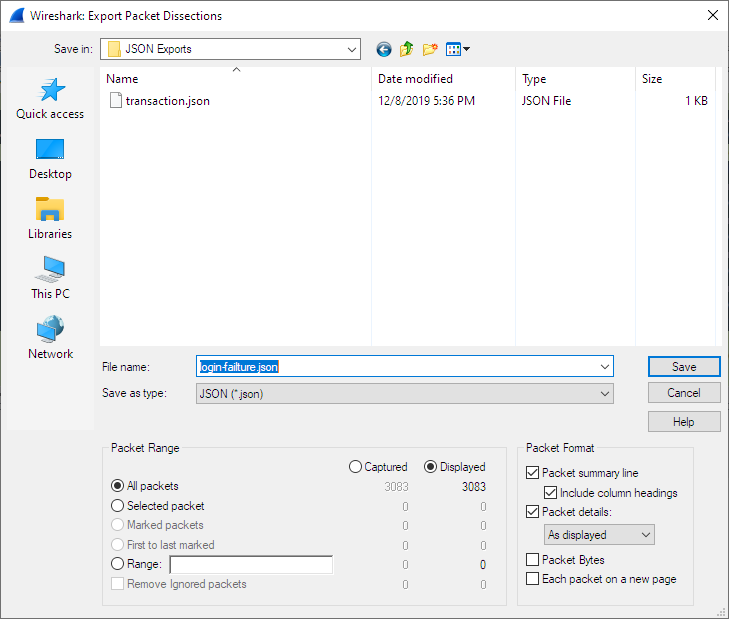
This lets you save the packet list, packet details, and packet bytes as plain text, CSV, JSON, and other formats.
The format can be selected from the “Export As” drop-down and further customized using the “Packet Range” and “Packet Format” controls. Some controls are unavailable for some formats, notably CSV and JSON. The following formats are supported:
- Plain text as shown in the main window
- Comma-separated values (CSV)
- C-compatible byte arrays
- PSML (summary XML)
- PDML (detailed XML)
- JavaScript Object Notation (JSON)
Here are some examples of exported data:
Plain text.
No. Time Source Destination Protocol Length SSID Info
1 0.000000 200.121.1.131 172.16.0.122 TCP 1454 10554 → 80 [ACK] Seq=1 Ack=1 Win=65535 Len=1400 [TCP segment of a reassembled PDU]
Frame 1: 1454 bytes on wire (11632 bits), 1454 bytes captured (11632 bits)
Ethernet II, Src: 00:50:56:c0:00:01, Dst: 00:0c:29:42:12:13
Internet Protocol Version 4, Src: 200.121.1.131 (200.121.1.131), Dst: 172.16.0.122 (172.16.0.122)
0100 .... = Version: 4
.... 0101 = Header Length: 20 bytes (5)
Differentiated Services Field: 0x00 (DSCP: CS0, ECN: Not-ECT)
Total Length: 1440
Identification: 0x0141 (321)
Flags: 0x0000
...0 0000 0000 0000 = Fragment offset: 0
Time to live: 106
Protocol: TCP (6)
Header checksum: 0xd390 [validation disabled]
[Header checksum status: Unverified]
Source: 200.121.1.131 (200.121.1.131)
Destination: 172.16.0.122 (172.16.0.122)
[Source GeoIP: PE, ASN 6147, Telefonica del Peru S.A.A.]
Transmission Control Protocol, Src Port: 10554, Dst Port: 80, Seq: 1, Ack: 1, Len: 1400
| Tip | |
|---|---|
|
If you would like to be able to import any previously exported packets from a plain text file it is recommended that you do the following:
|
CSV.
"No.","Time","Source","Destination","Protocol","Length","SSID","Info","Win Size" "1","0.000000","200.121.1.131","172.16.0.122","TCP","1454","","10554 > 80 [ACK] Seq=1 Ack=1 Win=65535 Len=1400 [TCP segment of a reassembled PDU]","65535" "2","0.000011","172.16.0.122","200.121.1.131","TCP","54","","[TCP ACKed unseen segment] 80 > 10554 [ACK] Seq=1 Ack=11201 Win=53200 Len=0","53200" "3","0.025738","200.121.1.131","172.16.0.122","TCP","1454","","[TCP Spurious Retransmission] 10554 > 80 [ACK] Seq=1401 Ack=1 Win=65535 Len=1400 [TCP segment of a reassembled PDU]","65535" "4","0.025749","172.16.0.122","200.121.1.131","TCP","54","","[TCP Window Update] [TCP ACKed unseen segment] 80 > 10554 [ACK] Seq=1 Ack=11201 Win=63000 Len=0","63000" "5","0.076967","200.121.1.131","172.16.0.122","TCP","1454","","[TCP Previous segment not captured] [TCP Spurious Retransmission] 10554 > 80 [ACK] Seq=4201 Ack=1 Win=65535 Len=1400 [TCP segment of a reassembled PDU]","65535"
JSON.
{
"_index": "packets-2014-06-22",
"_type": "doc",
"_score": null,
"_source": {
"layers": {
"frame": {
"frame.encap_type": "1",
"frame.time": "Jun 22, 2014 13:29:41.834477000 PDT",
"frame.offset_shift": "0.000000000",
"frame.time_epoch": "1403468981.834477000",
"frame.time_delta": "0.450535000",
"frame.time_delta_displayed": "0.450535000",
"frame.time_relative": "0.450535000",
"frame.number": "2",
"frame.len": "86",
"frame.cap_len": "86",
"frame.marked": "0",
"frame.ignored": "0",
"frame.protocols": "eth:ethertype:ipv6:icmpv6",
"frame.coloring_rule.name": "ICMP",
"frame.coloring_rule.string": "icmp || icmpv6"
},
"eth": {
"eth.dst": "33:33:ff:9e:e3:8e",
"eth.dst_tree": {
"eth.dst_resolved": "33:33:ff:9e:e3:8e",
"eth.dst.oui": "3355647",
"eth.addr": "33:33:ff:9e:e3:8e",
"eth.addr_resolved": "33:33:ff:9e:e3:8e",
"eth.addr.oui": "3355647",
"eth.dst.lg": "1",
"eth.lg": "1",
"eth.dst.ig": "1",
"eth.ig": "1"
},
"eth.src": "00:01:5c:62:8c:46",
"eth.src_tree": {
"eth.src_resolved": "00:01:5c:62:8c:46",
"eth.src.oui": "348",
"eth.src.oui_resolved": "Cadant Inc.",
"eth.addr": "00:01:5c:62:8c:46",
"eth.addr_resolved": "00:01:5c:62:8c:46",
"eth.addr.oui": "348",
"eth.addr.oui_resolved": "Cadant Inc.",
"eth.src.lg": "0",
"eth.lg": "0",
"eth.src.ig": "0",
"eth.ig": "0"
},
"eth.type": "0x000086dd"
},
"ipv6": {
"ipv6.version": "6",
"ip.version": "6",
"ipv6.tclass": "0x00000000",
"ipv6.tclass_tree": {
"ipv6.tclass.dscp": "0",
"ipv6.tclass.ecn": "0"
},
"ipv6.flow": "0x00000000",
"ipv6.plen": "32",
"ipv6.nxt": "58",
"ipv6.hlim": "255",
"ipv6.src": "2001:558:4080:16::1",
"ipv6.addr": "2001:558:4080:16::1",
"ipv6.src_host": "2001:558:4080:16::1",
"ipv6.host": "2001:558:4080:16::1",
"ipv6.dst": "ff02::1:ff9e:e38e",
"ipv6.addr": "ff02::1:ff9e:e38e",
"ipv6.dst_host": "ff02::1:ff9e:e38e",
"ipv6.host": "ff02::1:ff9e:e38e",
"ipv6.geoip.src_summary": "US, ASN 7922, Comcast Cable Communications, LLC",
"ipv6.geoip.src_summary_tree": {
"ipv6.geoip.src_country": "United States",
"ipv6.geoip.country": "United States",
"ipv6.geoip.src_country_iso": "US",
"ipv6.geoip.country_iso": "US",
"ipv6.geoip.src_asnum": "7922",
"ipv6.geoip.asnum": "7922",
"ipv6.geoip.src_org": "Comcast Cable Communications, LLC",
"ipv6.geoip.org": "Comcast Cable Communications, LLC",
"ipv6.geoip.src_lat": "37.751",
"ipv6.geoip.lat": "37.751",
"ipv6.geoip.src_lon": "-97.822",
"ipv6.geoip.lon": "-97.822"
}
},
"icmpv6": {
"icmpv6.type": "135",
"icmpv6.code": "0",
"icmpv6.checksum": "0x00005b84",
"icmpv6.checksum.status": "1",
"icmpv6.reserved": "00:00:00:00",
"icmpv6.nd.ns.target_address": "2001:558:4080:16:be36:e4ff:fe9e:e38e",
"icmpv6.opt": {
"icmpv6.opt.type": "1",
"icmpv6.opt.length": "1",
"icmpv6.opt.linkaddr": "00:01:5c:62:8c:46",
"icmpv6.opt.src_linkaddr": "00:01:5c:62:8c:46"
}
}
}
}
}
]
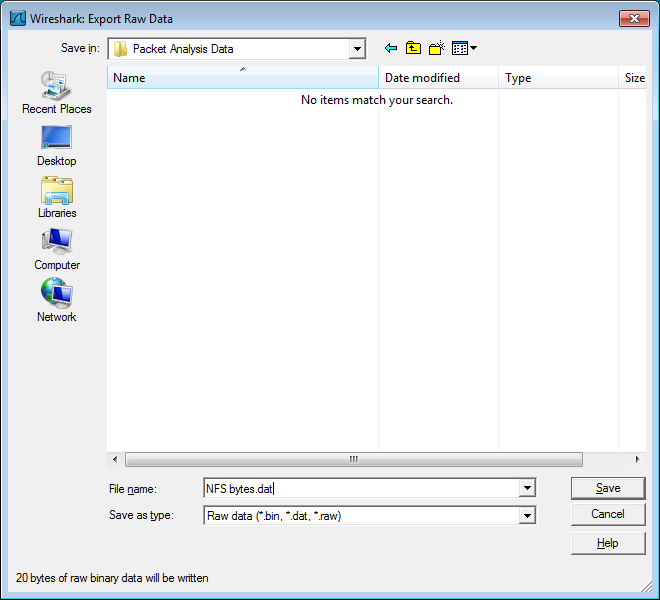
Export the bytes selected in the “Packet Bytes” pane into a raw binary file.
- File name
- The file name to export the packet data to.
- Save as type
- The file extension.
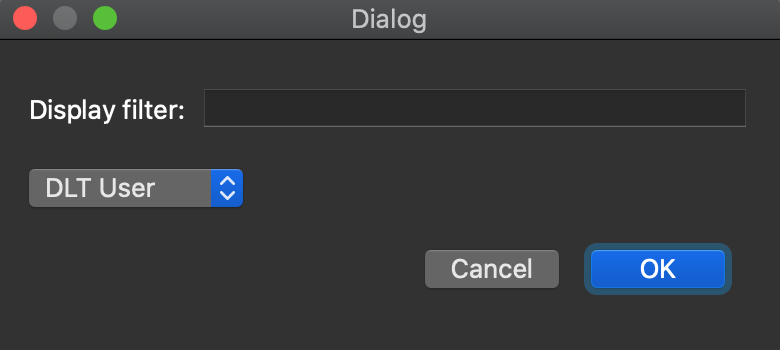
The “Export PDUs to File…” dialog box allows you to filter the captured Protocol Data Units (PDUs) and export them into the file. It allows you to export reassembled PDUs avoiding lower layers such as HTTP without TCP, and decrypted PDUs without the lower protocols such as HTTP without TLS and TCP.
-
In the main menu select → . Wireshark will open a corresponding dialog Figure 5.13, “Export PDUs to File window”.
-
To select the data according to your needs, optionally type a filter value into the
Display Filterfield. For more information about filter syntax, see the Wireshark Filters man page. -
In the field below the
Display Filterfield you can choose the level from which you want to export the PDUs to the file. There are seven levels:-
DLT User. You can export a protocol, which is framed in the user data link type table without the need to reconfigure the DLT user table. For more information, see the How to Dissect Anything page. -
DVB-CI. You can use it for the Digital Video Broadcasting (DVB) protocol. -
LogcatandLogcat Text. You can use them for the Android logs. -
OSI layer 3. You can use it to export PDUs encapsulated in the IPSec or SCTP protocols. -
OSI layer 4. You can use it to export PDUs encapsulated in the TCP or UDP protocols. -
OSI layer 7. You can use it to export the following protocols: CredSSP over TLS, Diameter, protocols encapsulated in TLS and DTLS, H.248, Megaco, RELOAD framing, SIP, SMPP.Note As a developer you can add any dissector to the existing list or define a new entry in the list by using the functions in
epan/exported_pdu.h.
-
- To finish exporting PDUs to file, click the button in the bottom-right corner. This will close the originally captured file and open the exported results instead as a temporary file in the main Wireshark window.
-
You may save the temporary file just like any captured file. See Section 5.3, “Saving Captured Packets” for details.
Note The file produced has a
Wireshark Upper PDUencapsulation type that has somewhat limited support outside of Wireshark, but is very flexible and can contain PDUs for any protocol for which there is a Wireshark dissector.
The “Strip Headers…” dialog box allows you to filter known encapsulation types on whatever protocol layer they appear and export them into a new capture file, removing lower-level protocols. It allows you to export reassembled packets and frames without lower layers such as GPF, GRE, GSE, GTP-U, MPLS, MPE, PPP, and more. If Wireshark has performed decryption, then you can export decrypted IP from protocols like IEEE 802.11 or IPSec without having to save encryption keys.
The procedure is similar to that of Section 5.7.4, “The “Export PDUs to File…” Dialog Box”:
- In the main menu select → . Wireshark will open a corresponding dialog.
-
To select the data according to your needs, optionally type a filter value into the
Display Filterfield. For more information about filter syntax, see the Wireshark Filters man page. -
In the field below the
Display Filterfield you can choose the encapsulation type you want to find and export to the file. There are two encapsulations supported:-
Ethernet. You can use it to export Ethernet encapsulated in other protocols. -
IP. You can use it to export IPv4 and IPv6 encapsulated in other protocols.Note As a developer you can add encapsulations to the list by using the functions in
epan/exported_pdu.h.
-
- To finish exporting to file, click the button in the bottom-right corner. This will close the originally captured file and open the exported results instead as a temporary file in the main Wireshark window.
-
You may save the temporary file just like any captured file. See Section 5.3, “Saving Captured Packets” for details.
Note The new capture files produced have standard encapsulation types and can be read in nearly any tool.
Transport Layer Security (TLS) encrypts the communication between a client and a server. The most common use for it is web browsing via HTTPS.
Decryption of TLS traffic requires TLS secrets. You can get them in the form of stored session keys in a "key log file", or by using an RSA private key file. For more details, see the TLS wiki page.
The → menu option generates a new "key log file" which contains TLS session secrets known by Wireshark. This feature is useful if you typically decrypt TLS sessions using the RSA private key file. The RSA private key is very sensitive because it can be used to decrypt other TLS sessions and impersonate the server. Session keys can be used only to decrypt sessions from the packet capture file. However, session keys are the preferred mechanism for sharing data over the Internet.
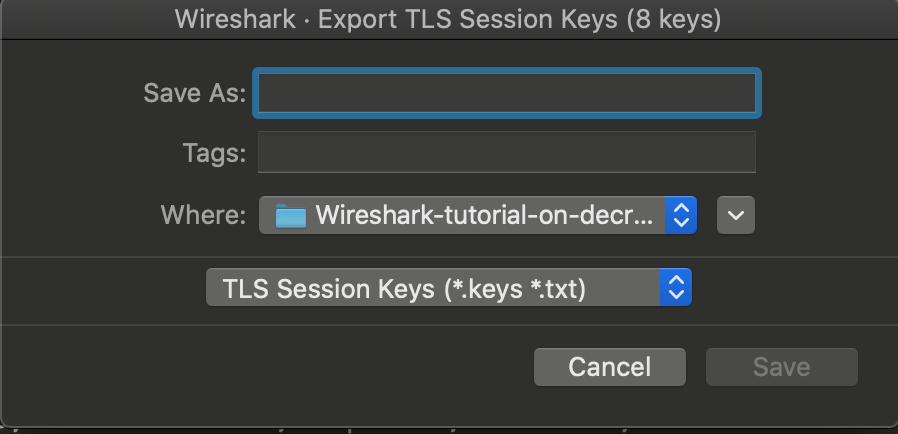
To export captured TLS session keys, follow the steps below:
-
In the main menu select → . Wireshark will open a corresponding dialog Figure 5.14, “Export TLS Session Keys window”.
-
Type the desired file name in the
Save Asfield. -
Choose the destination folder for your file in the
Wherefield. - Press the button to complete the export file procedure.
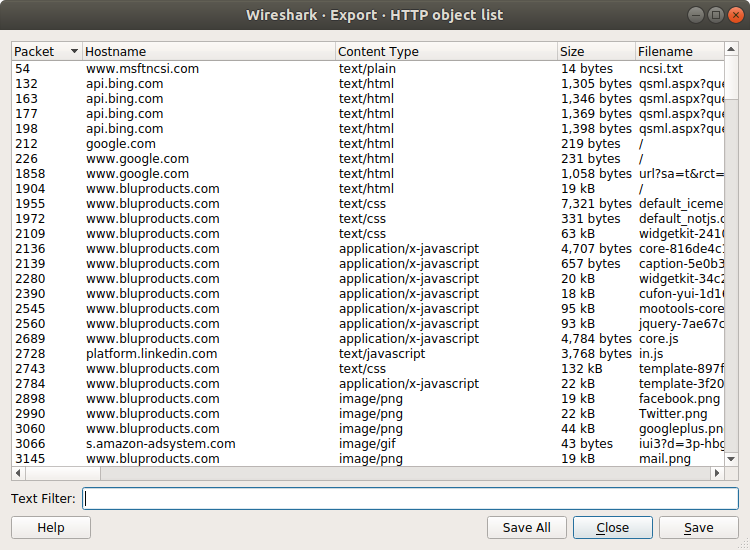
This feature scans through the selected protocol’s streams in the currently open capture file or running capture and allows the user to export reassembled objects to the disk. For example, if you select HTTP, you can export HTML documents, images, executables, and any other files transferred over HTTP to the disk. If you have a capture running, this list is automatically updated every few seconds with any new objects seen. The saved objects can then be opened or examined independently of Wireshark.
Columns:
- Packet
- The packet number in which this object was found. In some cases, there can be multiple objects in the same packet.
- Hostname
- The hostname of the server that sent this object.
- Content Type
- The content type of this object.
- Size
- The size of this object in bytes.
Filename: The filename for this object. Each protocol generates the filename differently. For example, HTTP uses the final part of the URI and IMF uses the subject of the email.
Inputs:
- Text Filter
- Only displays objects containing the specified text string.
- Help
- Opens this section of the “User’s Guide”.
- Save All
- Saves all objects (including those not displayed) using the filename from the filename column. You will be asked what directory or folder to save them in.
- Close
- Closes the dialog without exporting.
- Save
- Saves the currently selected object as a filename you specify. The default filename to save as is taken from the filename column of the objects list.